The right balance between on-premise and online security can make all the difference in protecting your valuable data and infrastructure.
On-site security systems offer the advantage of keeping your data physically nearby, which can give you more control and security. Security systems enable physical security with devices directly monitored by your employees. This proximity ensures that any immediate threat can be dealt with quickly and efficiently.
Online security, on the other hand, offers flexibility and scalability, which are crucial for growing companies. Cloud solutions ensure that data and applications are accessible from anywhere, promoting seamless continuity of operations. Balancing the two will yield long-term benefits.
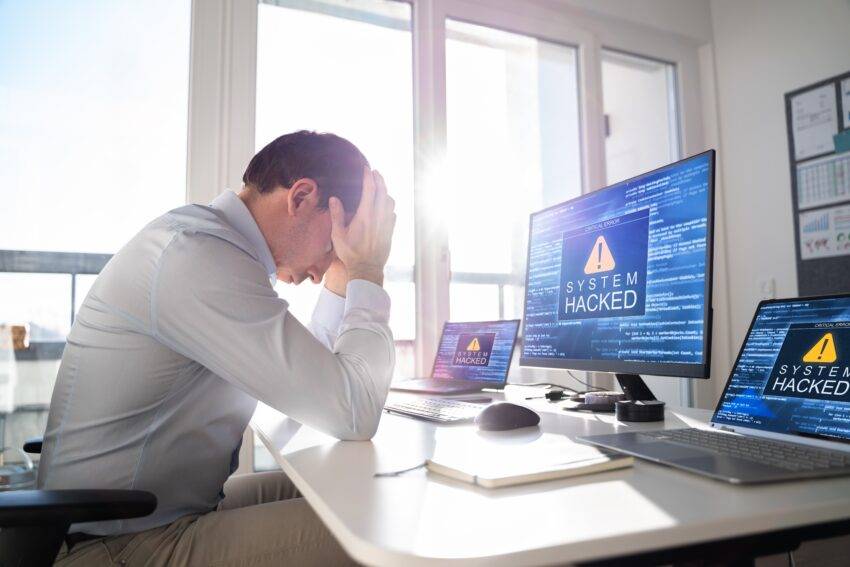
Understanding the cybersecurity threats faced by UK SMEs
Small and medium-sized companies are increasingly being targeted by cyberattacks due to their perceived vulnerabilities. Understanding threats like ransomware and phishing is critical to implementing effective security solutions.
The rise of SMB cyberattacks
Cyber attacks on SMBs have increased significantly and pose a major threat to their operations, data and revenue. Many companies are expressing increased concern about cyber threats influenced by high-profile cyber attacks.
Attackers often see SMEs as easy targets because they may lack robust security measures. The most common threats include ransomware, which encrypts data to extort ransoms, and phishing, which aims to steal sensitive information. Organizations must recognize these threats to prioritize their security needs and invest in better protection measures.
Importance of comprehensive security
Implementing layers of security ensures that pitfalls in an area do not result in a security breach. It is critical to keep software up to date, use strict access controls, and actively monitor networks. Many UK businesses report struggling to keep up with evolving cyber threats. Focus on integrating advanced security solutions such as encryption and multi-factor authentication. By addressing both internal and external vulnerabilities, you create a resilient cybersecurity posture.
Building a robust on-premise and online security infrastructure
To secure a small to medium-sized business, a comprehensive strategy that integrates both on-premise systems and online solutions is critical. Key components include designing an effective network architecture, integrating cloud and SaaS solutions, and maintaining secure communication channels.
Designing a secure network architecture
When building a secure network, start with a basic component: the firewall. It acts as the first line of defense and prevents unauthorized access. Implementing endpoint protection across all devices is essential to protect against malware and unauthorized intrusions. Consider deploying SD-WAN technology to improve connectivity and improve security across distributed networks.
Network security should also include strict access controls to ensure that only authorized personnel have permissions.
Integrate Video surveillance for monitoring premises efficient – this increases security against physical threats by enabling real-time observation. Ultimately, the design should anticipate potential risks and include multiple layers of defense.
Integration of cloud and SaaS solutions
Incorporating cloud technology contributes to a scalable and flexible approach to security. When integrating cloud solutions and SaaS, prioritize cloud security measures to protect data stored online. This includes robust encryption methods and secure data storage practices.
Choose solutions that offer comprehensive security solutions with automatic updates to patch vulnerabilities as they are discovered.
Use SaaS solutions that include integrated security configurations to further protect against online phishing scams. Authentication through QR codes can enable secure access management and serve as protection against unauthorized access.
Maintaining secure channels
Secure communication channels protect sensitive information between employees and external partners. Employ encryption protocols to protect all data in transit and ensure VPNs are used to encrypt traffic between remote workers and the main office.
Implementing secure authentication methods is critical. Use a QR scanner app for secure and quick login processes without sacrificing convenience. Conduct regular security audits to identify vulnerabilities in IT infrastructure. Staying vigilant and regularly updating systems can help prevent breaches and maintain confidence in your security system.
Important security measures and best practices
Setting up a robust security system for your small or medium-sized business requires implementing multi-factor authentication and strict security policies. These measures ensure better protection against unauthorized access and data breaches.
Implementation of multi-factor authentication
Multi-factor authentication (MFA) significantly increases security by requiring users to identify themselves multiple times before accessing sensitive systems. This method may include a combination of passwords, security tokens, or biometric verification to ensure only authorized individuals gain access.
Integrating MFA into your security plan helps reduce the risk of unauthorized access. It adds an additional layer of security beyond the traditional password Protection. MFA also supports compliance with regulatory standards. Maintaining your systems to ensure MFA functionality is critical as it protects against new threats. MFA complements other security measures such as anti-malware solutions and endpoint security.
Establish strict security guidelines
Strong security policies form the foundation of an organization’s defense strategy. These policies should be comprehensive and cover aspects such as password security, maintenance and email security. Clear policies help employees understand their responsibilities in adhering to company safety standards.
Password policies should require complex passwords and regular updates to reduce the likelihood of breaches. Firewalls and encryption provide protection by securing data transmission and storage.
Enforcing regular training promotes compliance. Establishing and communicating these policies ensures your employees are informed and alert to security threats. Effective policies also help ensure regulatory compliance, protect your organization from legal risks, and improve your organization’s overall security posture.
Ensuring continuous protection and reliability
Establishing a robust security system requires constant attention to both infrastructure and practices. Regular security audits and strategic business continuity planning help protect against data breaches and ensure reliability.
Conducting regular security audits
Regular security audits are a critical component of maintaining your organization’s cybersecurity. These audits include a thorough examination of your network and systems to identify vulnerabilities. Invest in accurate app security testing is critical, especially given evolving technological threats. By integrating security into development processes, for example by introducing a DevSecOps approach, the effectiveness of security can be increased.
Assess endpoint security measures regularly. Make sure every device connected to your network follows security protocols. Identifying and remediating vulnerabilities early reduces the likelihood of data breaches.
Planning for business continuity
Business continuity planning requires creation a comprehensive plan that takes potential risks into account such as data breaches and system failures. Investing in robust cybersecurity infrastructure and maintenance practices is critical for long-term resilience.
Consider remote work strategies to improve business agility in the event of unexpected events. Implement redundant systems and data backups to further protect against catastrophic data loss. This type of investment in business continuity not only strengthens the reliability of your company, but also protects your assets and reputation. By regularly reviewing and updating this plan, you can adapt it to changing business needs and technological advances.
Diploma
To set up a comprehensive security system for your SMB, you need to combine on-premise and cloud solutions. An effective approach ensures data protection, reduces risks and increases operational efficiency.
By thoughtfully integrating these systems, you can improve your SMB’s defenses while maintaining adaptability and control over sensitive information. This strategic combination allows you to effectively protect your assets.